-min.webp)
Phishing campaigns that "live off the land" of trusted SaaS platforms have become one of the most reliable ways for attackers to slip past Secure Email Gateways (SEGs). When a malicious email originates from a domain like business.facebook.com or facebookmail.com, SPF, DKIM, and DMARC all line up cleanly, sender reputation is pristine, and most filters wave it through. Identifying these messages as phishing requires a deeper level of investigation that is often not feasible to perform there.
Across multiple Prophet AI customers, we've been investigating a wave of these alerts tied to a campaign abusing Meta's own Business Manager partner-invitation infrastructure. The emails are genuine Meta notifications, sent from genuine Meta servers, but the partner request was created by an attacker, and the link inside leads to a credential-harvesting page dressed up as the Meta Agency Partner Program.
This is the same playbook as the Zoom TOAD attack we wrote about in January, applied to a different trusted brand, and another great example of why phishing investigations need to look at intent, not just headers.
The mechanics are simple, which is part of what makes them effective:
The clever piece is step three. The attacker never has to spoof Meta. Meta does the sending for them. Every reputation check, every authentication header, every "is this really from Facebook?" heuristic comes back clean, because the email genuinely is from Facebook. The malicious payload is a single off-domain link buried inside an otherwise authentic notification.
{{ebook-cta}}
Is there any vulnerability being exploited in this case? Not the typical "CVE-like" vulnerability, but a process/business one. Meta's processes around Business account creation and partner requests are being exploited to send a malicious link via a trusted source.
For a marketing agency or in-house social team, the request looks normal in context. Partner invitations are a routine part of how Business Manager works. Someone clicks "View request," authenticates on what looks like a Meta page, and the attacker walks away with access to ad accounts, Pages, pixels, and payment methods, sometimes for the victim's organization, sometimes for every client that agency manages. That secondary blast radius is closer in shape to BEC than to traditional credential phishing: one compromised partner approval opens a portfolio.
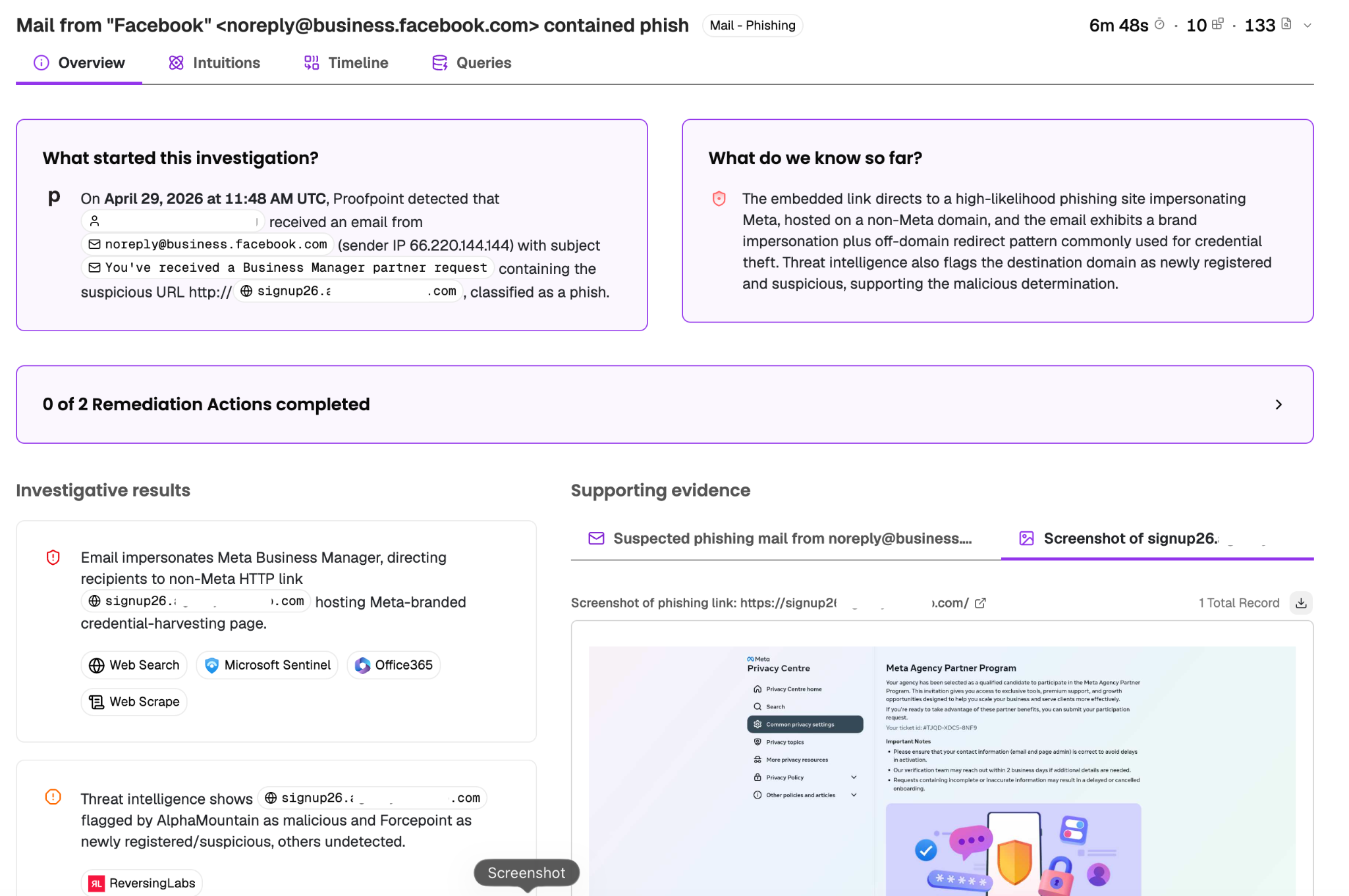
In one recent case, Proofpoint flagged an inbound email to a customer's user with the subject "You've received a Business Manager partner request," sent from noreply@business.facebook.com (sender IP 66.220.144.144, which is genuinely Meta's). The embedded URL pointed to hxxp://signup26[.]agency-ad-hub[.]com.
A traditional triage process would run into the same wall the gateway did. Sender domain: trusted. Authentication: passing. Subject line: a real Meta notification template. On surface signals alone, there's nothing wrong with this email.
Prophet AI's investigation went a layer deeper:
Prophet AI ran 133 queries across 10 data sources and reached a verdict in under seven minutes, classifying the email as a phish, surfacing the supporting evidence, and queuing the remediation actions for analyst review. This is the same pattern of investigation depth that catches campaigns the perimeter doesn't.
The Meta Business Manager variant is a particularly clean case study in why "trusted sender" is no longer a meaningful signal on its own.
Three things make this campaign worth paying attention to:
The infrastructure is real. Unlike most brand impersonation, there is no spoofed domain to detect, no header to validate, no DKIM signature to fail. The email is exactly what it claims to be, and the only malicious component is the destination of one link. Any control that operates on sender identity is going to pass this through.
The blast radius is large. Marketing agencies running Business Manager for dozens of clients are a single point of failure. One account manager approving a fraudulent partner request can expose every client portfolio under that agency. Enterprises with regional Business Manager hierarchies face the same shape of risk. The attacker doesn't need to break into the company's infrastructure, they need one person with the right permissions to click "View request."
Detection has to happen at and after the URL. Because the email itself is structurally legitimate, the only place to catch this campaign is the embedded link. It has to be checked against threat intel that's fresh enough to know about a domain registered days ago. Stale feeds will miss it. So will any analyst process that stops at "the headers check out."
This is exactly the type of investigation that confuses a junior analyst working from a static playbook. The "obvious" indicators all point to safe. The actual signal is a destination domain that doesn't match the brand the email is claiming to be from, registered in the last week, hosting a credential harvester, and it only surfaces if someone (or something) looks past the envelope and reasons about intent.
Attackers are increasingly building campaigns specifically designed to ride on the reputation of platforms users already trust. Zoom OTP emails. PayPal invoices. DocuSign envelopes. Google Calendar invites. And now Meta Business Manager partner requests. The pattern is the same: use the platform's own infrastructure to deliver an email that passes every sender-reputation check, and put the malicious payload somewhere the gateway won't look.
Defending against this class of attack requires investigations that go beyond "did the email authenticate?" and ask "does the content match the sender, does the destination match the brand, and is the infrastructure on the other side of that link something we've ever seen before?" That's a level of reasoning that doesn't fit cleanly into the typical L1 alert triage playbook, and at the volume of reported phishing alerts modern SOCs see, the contributing alert fatigue makes it unrealistic to escalate every one of them to L2.
This is where Prophet AI fits. By running the full phishing investigation, header analysis, link analysis, threat intel pivots, infrastructure reputation, page content review, cross-tool correlation, at machine speed on every reported phishing alert, Prophet AI gives security teams the ability to run deep investigations at the throughput of an automated triage queue. Campaigns like this Meta Business Manager wave get caught on arrival, with the supporting evidence already assembled for the analyst who signs off on remediation.
If you're seeing a spike in Meta-themed phishing reports across your environment, you're not alone. Make sure your investigation process is prepared to keep up with attackers who have been figuring out how to identify and exploit trusted email sources like Zoom and Meta.
This guide breaks down how AI SOC agents work and how to build an agile security operation around agentic AI